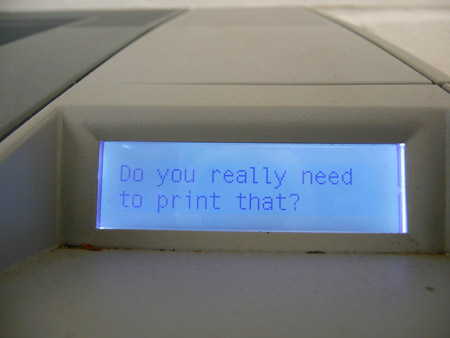

This is not difficult to do, once you know how. Of course, it’s not terribly useful, since a) most people don’t read the display on a printer unless an error occurs, or b) you’re only likely to see it once you’ve already sent something to print.
Is this kind of very, very weak persuasion – actually worthwhile? From a user’s point of view, it’s less intrusive than, say, a dialogue box that asks “Are you sure you want to print that? Think of the environment” every time you try to print something (which would become deeply irritating for many users), but when applied thoughtfully, as (in a different area of paper consumption) in Pete Kazanjy’s These Come From Trees initiative, or even in various e-mail footers* (below), there may actually be some worthwhile influence on user behaviour. It’s not ‘micropersuasion’ in Steve Rubel’s sense, exactly, but there is some commonality.
I’m thinking that addressing the choices users make when they decide to print (or not print) a document or email could be an interesting specific example to investigate as part of my research, once I get to the stage of user trials. How effective are the different strategies in actually reducing paper/energy/toner/fuser/ink consumption and waste generation? Would better use of ‘Printer-friendly’ style sheets for webpages save a lot of unnecessary reprints due to cut-off words and broken layouts? Should, say, two pages per sheet become the default when a dicument goes above a certain number of pages? Should users be warned if widows (not so much orphans) are going to increase the number of sheets needed, or should the leading be automatically adjusted (by default) to prevent this? What happens if we make it easier to avoid printing banner ads and other junk? What happens if we make the paper tray smaller so the user is reminded of just how much paper he/she is getting through? What happens if we include a display showing the cost (financially) of the toner/ink, paper and electricity so far each day, or for each user? What happens if we ration paper for each user and allow him or her to ‘trade’ with other users? What happens if we give users a ‘reward’ for reaching targets of reducing printer usage, month-on-month? And so on. (The HP MOPy Fish – cited in B J Fogg’s Persuasive Technology – is an example of the opposite intention: a system designed to encourage users to print more, by rewarding them.)
Printing is an interesting area, since it allows the possibility of testing out both software and hardware tactics for causing behaviour change, which I’m keen to do.